Vulnerability Overview
The Vulnerability Overview provides a consolidated view of known vulnerabilities affecting your external infrastructure. It aggregates data from port scans, technology detection, and CVE matching to show which of your external assets have known vulnerabilities, prioritized for action.
Overview
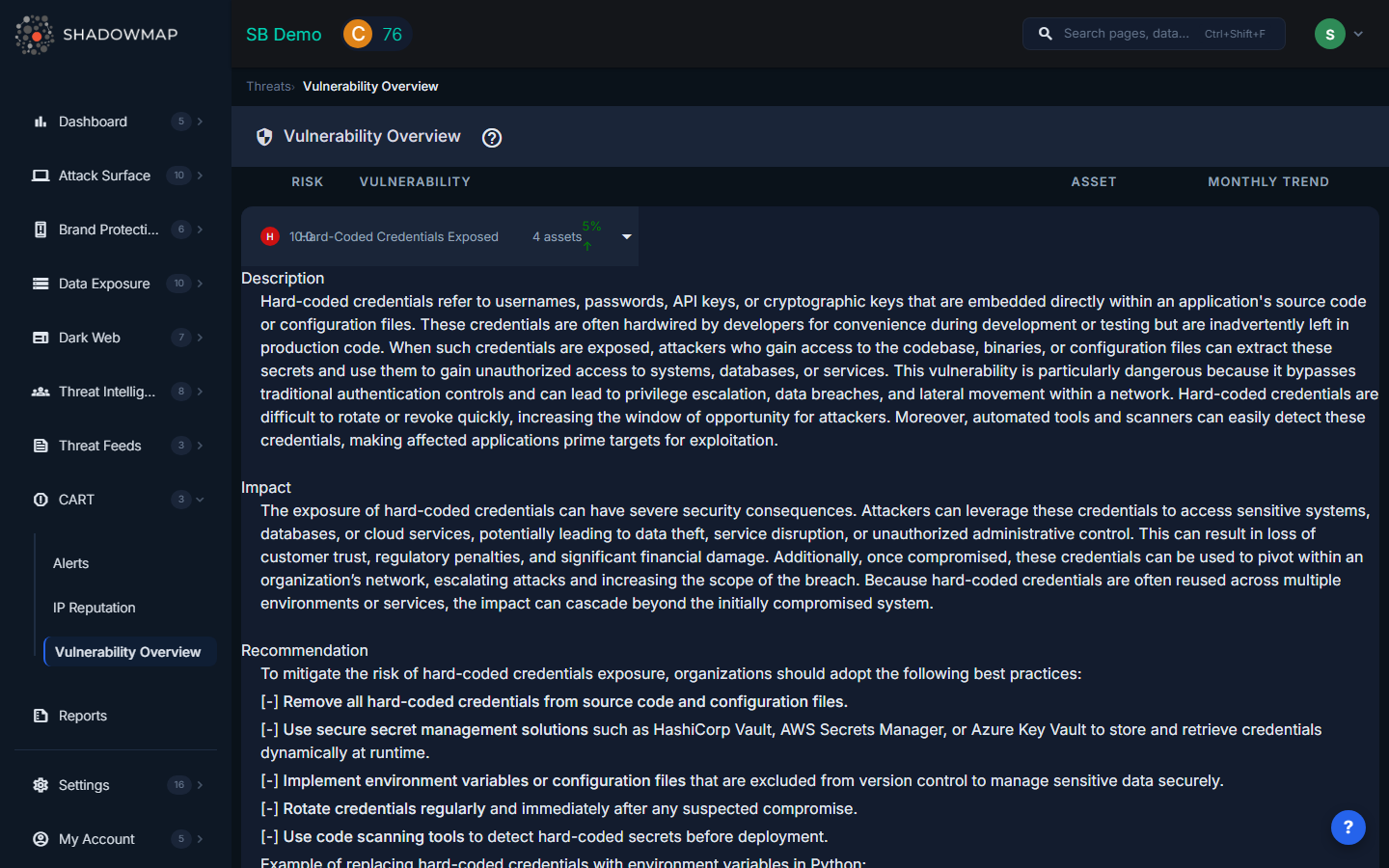
This view presents vulnerability data with prioritization indicators, allowing your team to focus remediation efforts on the most dangerous and exploitable issues first.
Prioritization Framework
Vulnerabilities are ranked using a multi-factor prioritization model:
| Factor | Description | Why It Matters |
|---|---|---|
| CVSS Score | Severity rating from the National Vulnerability Database (0.0--10.0) | Industry-standard measure of vulnerability severity -- Critical (9.0+), High (7.0--8.9), Medium (4.0--6.9), Low (0.1--3.9) |
| KEV Status | Whether the vulnerability appears in CISA's Known Exploited Vulnerabilities catalog | KEV entries represent vulnerabilities that are actively being exploited in the wild -- these demand immediate attention |
| Exploit Availability | Whether public exploit code or proof-of-concept exists | Publicly available exploits dramatically lower the barrier for attackers. A high-CVSS vulnerability with a public exploit is far more dangerous than one without |
| Asset Criticality | The importance of the affected asset to your organization | A medium-severity vulnerability on a payment processing server is more urgent than a critical vulnerability on a development test server |
How Vulnerabilities Are Detected
ShadowMap identifies vulnerabilities through a multi-step process:
- Port scanning discovers open services on your external IP addresses
- Technology fingerprinting identifies the software and versions running on each service
- CVE matching correlates detected software versions against the National Vulnerability Database
- Enrichment adds KEV status, exploit availability, and EPSS probability scores
Vulnerability vs. CVE Intelligence
| Vulnerability Overview (this page) | CVEs (Threat Intelligence) | |
|---|---|---|
| Scope | Vulnerabilities confirmed on YOUR assets | Global CVE database across all software |
| Data source | ShadowMap scans of your infrastructure | NVD, MITRE, and threat intelligence feeds |
| Use case | Remediation prioritization for your specific environment | Research and awareness of vulnerabilities in technologies you use |
Recommended Workflow
- Start with KEV-flagged vulnerabilities -- these are actively exploited and represent the highest immediate risk
- Address Critical CVSS scores next, especially those with available public exploits
- Consider asset criticality -- prioritize internet-facing production servers over internal test systems
- Cross-reference with IP Addresses to understand which infrastructure is affected
- Track remediation through the Alerts module to ensure vulnerabilities are patched within SLA targets
- Configure vulnerability scan profiles in Settings to control scan behavior and rate limits
