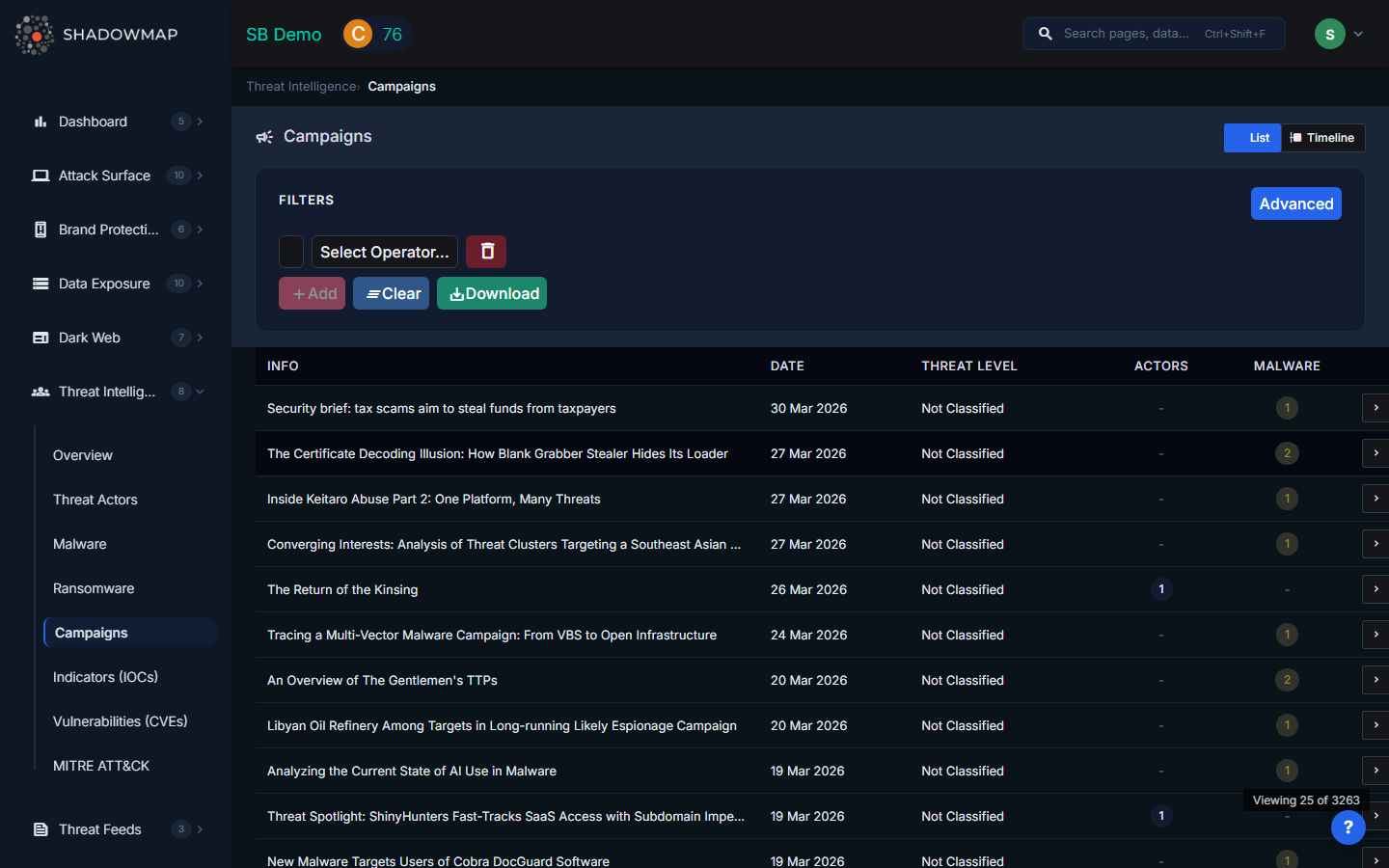
Campaigns
ShadowMap tracks active and historical attack campaigns, linking them to threat actors, malware, targeted industries, and timelines. A campaign represents a coordinated series of attacks with a shared objective -- understanding campaigns helps your team see the bigger picture beyond individual IOCs and connect disparate indicators into a coherent threat narrative.
Overview
View Modes
The page supports two views, toggled via buttons in the header:
- List View -- Sortable table with columns for bulk review and filtering. This is the default view.
- Timeline View -- Visual chronological timeline showing campaigns plotted by date. Best for understanding temporal patterns and briefing stakeholders.
Understanding the Data (List View)
| Column | Description |
|---|---|
| Info | Campaign name or description -- typically references the operation name, targeted industry, or attack method |
| Date | When the campaign was active or first reported |
| Threat Level | Severity assessment: High, Medium, Low, or Undefined |
| Actors | Count of threat actors attributed to this campaign (displayed as a tag; click through for details) |
| Malware | Count of malware families used in this campaign (displayed as a tag; click through for details) |
Click any row to view the full campaign details, including the complete list of associated threat actors, malware, IOCs, targeted sectors, and a narrative description.
Filters
Use the filter bar in List View to narrow results:
| Filter | Options |
|---|---|
| Threat Level | Filter by campaign severity (High, Medium, Low) |
| Organization | Filter by the reporting organization that attributed the campaign |
| Search | Free-text search across campaign names and descriptions |
Export
Click the export button to download the current filtered list view as an Excel file. The export respects all applied filters and search terms.
Timeline View
The timeline visualization displays campaigns as events on a horizontal axis, giving you:
- Temporal clustering -- See when campaign activity peaks and whether your sector is being targeted in waves
- Trend identification -- Identify whether campaign frequency is increasing or decreasing over time
- Briefing material -- The timeline format is effective for executive presentations and board reports
How to Use Campaign Intelligence
Threat Assessment
When a new campaign is reported that targets your industry:
- Check the threat actors involved -- are they known to target your region?
- Review the malware used -- do you have detection coverage for those families?
- Check the campaign's IOCs against your environment using IOC Search
- Map the campaign's techniques to your ATT&CK coverage to identify gaps
Proactive Defense
- Hunt -- Use campaign IOCs and TTPs to proactively search your SIEM and EDR for signs of compromise
- Harden -- If a campaign exploits specific vulnerabilities, prioritize patching those CVEs
- Detect -- Build detection rules covering the techniques used in campaigns targeting your sector
- Brief -- Provide your security team with campaign summaries so they know what to watch for
Incident Correlation
During an active investigation, search campaigns for matching:
- Malware families observed in your environment
- IOCs from your forensic analysis
- TTPs matching the attacker's behavior
Matching an incident to a known campaign provides attribution context and helps predict the attacker's next steps.
Related
- Threat Actors -- Groups behind campaigns
- Malware -- Tools used in campaigns
- Indicators of Compromise -- IOCs from campaign investigations
- MITRE ATT&CK -- Technique mapping for campaign TTPs
- Threat Intelligence Overview -- Recent campaigns widget on the dashboard
