SLA Violations
The SLA Violations view tracks findings that have exceeded their defined Service Level Agreement response times. SLA policies define how quickly findings of each severity level should be acknowledged and resolved, and this view surfaces all findings currently in breach of those timers.
Overview
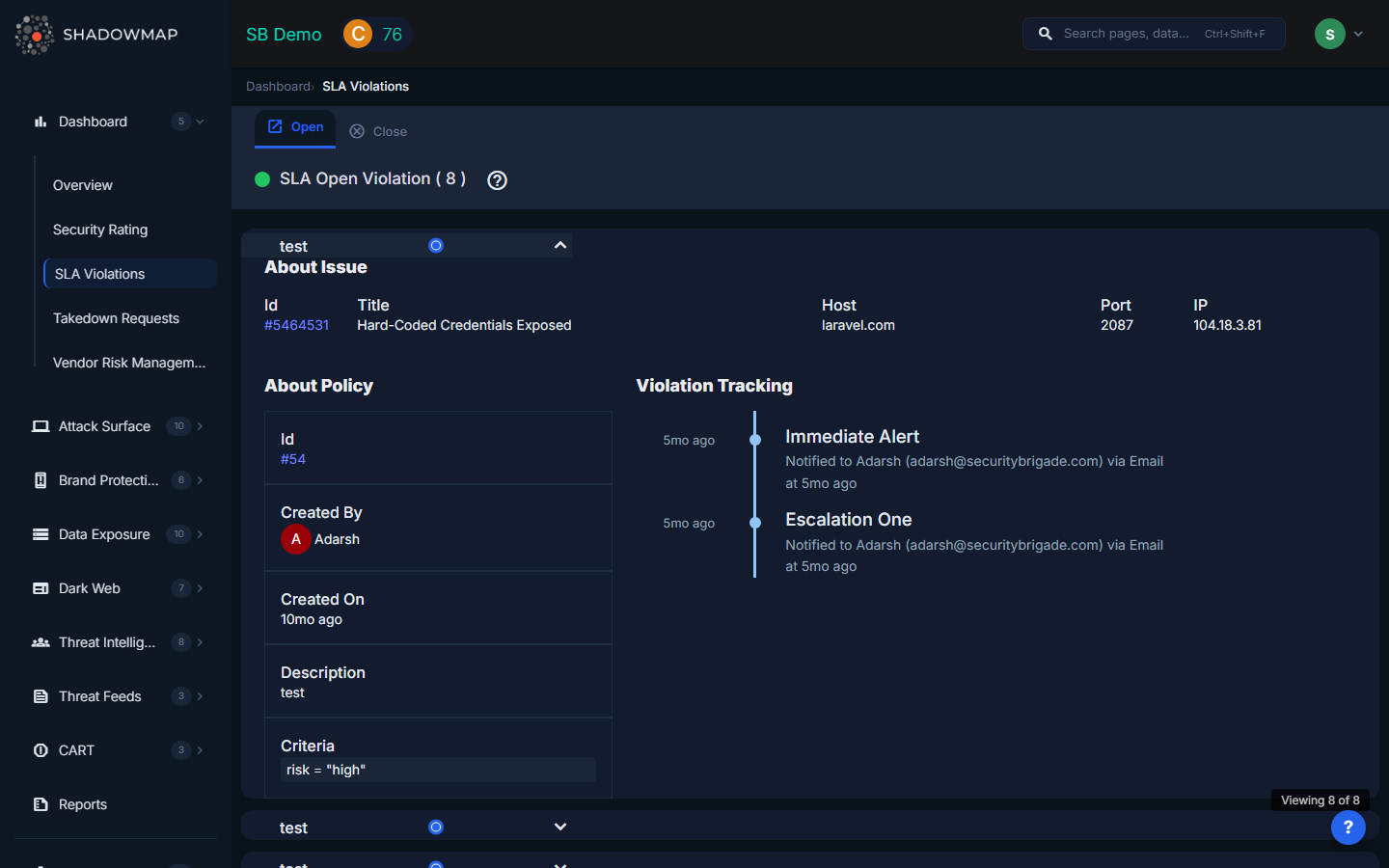
The page displays SLA violations as expandable accordion cards, loaded progressively as you scroll. The page header shows the total count of violations, and a scroll position indicator at the bottom tracks your position in the list.
Open vs. Closed Violations
SLA violations are separated into two views accessible from the navigation:
| View | Description |
|---|---|
| Open Violations | Findings that are currently past their SLA target and have not yet been resolved. These require immediate attention. |
| Closed Violations | Findings that were in SLA violation but have since been resolved. Useful for measuring historical SLA adherence and identifying patterns. |
Violation Cards
Each violation is displayed as a collapsible card containing:
| Field | Description |
|---|---|
| Policy Name | The SLA policy that was violated (links to the policy definition) |
| Finding Title | The specific finding that exceeded the SLA timeline |
| Severity | The severity level of the finding (Critical, High, Medium, Low) |
| Status | Current status of the violation (Open or Closed) |
| Triggered Time | When the SLA timer was exceeded -- the moment the violation was triggered |
| Resolution Time | For closed violations, when the finding was resolved. For open violations, shows time elapsed since the breach. |
| Assignee | The team or individual responsible for the finding |
SLA Target Examples
The actual SLA targets are configured by your organization's admin under Settings > SLA Policies. Typical targets might include:
| Severity | Acknowledge Within | Resolve Within |
|---|---|---|
| Critical | 4 hours | 24 hours |
| High | 24 hours | 7 days |
| Medium | 72 hours | 30 days |
| Low | 7 days | 90 days |
TIP
These are examples only. Your organization's actual SLA targets are defined in your SLA policy configuration.
Taking Action on Violations
For each open SLA violation:
- Click the violation card to expand it and see full details
- Navigate to the finding by clicking the finding title or link
- Investigate the finding -- determine root cause and remediation steps
- Update the finding status -- changing status to "Resolved" or another terminal state stops the SLA timer
- Add comments explaining any delay or documenting your remediation plan
Creating SLA Policies
If no SLA policies are configured, the page shows an empty state with a link to create your first policy. Navigate to Settings > SLA Policies to define response time targets by severity level.
Monitoring SLA Performance
Use the SLA Violations view to:
- Track response time compliance -- Are findings being addressed within policy targets?
- Identify bottlenecks -- Which severity levels or teams consistently breach SLA?
- Report to leadership -- Closed violation history provides data for security program maturity reports
- Improve processes -- Patterns in SLA breaches may indicate staffing gaps, tool gaps, or unclear ownership
