Discussions
ShadowMap monitors dark web forums for discussions that mention your organization, brand, domains, or key personnel. These forums are where threat actors coordinate attacks, sell access, share vulnerabilities, and trade stolen data. Early detection of these mentions gives your security team a critical window to prepare defenses before an attack materializes.
Overview
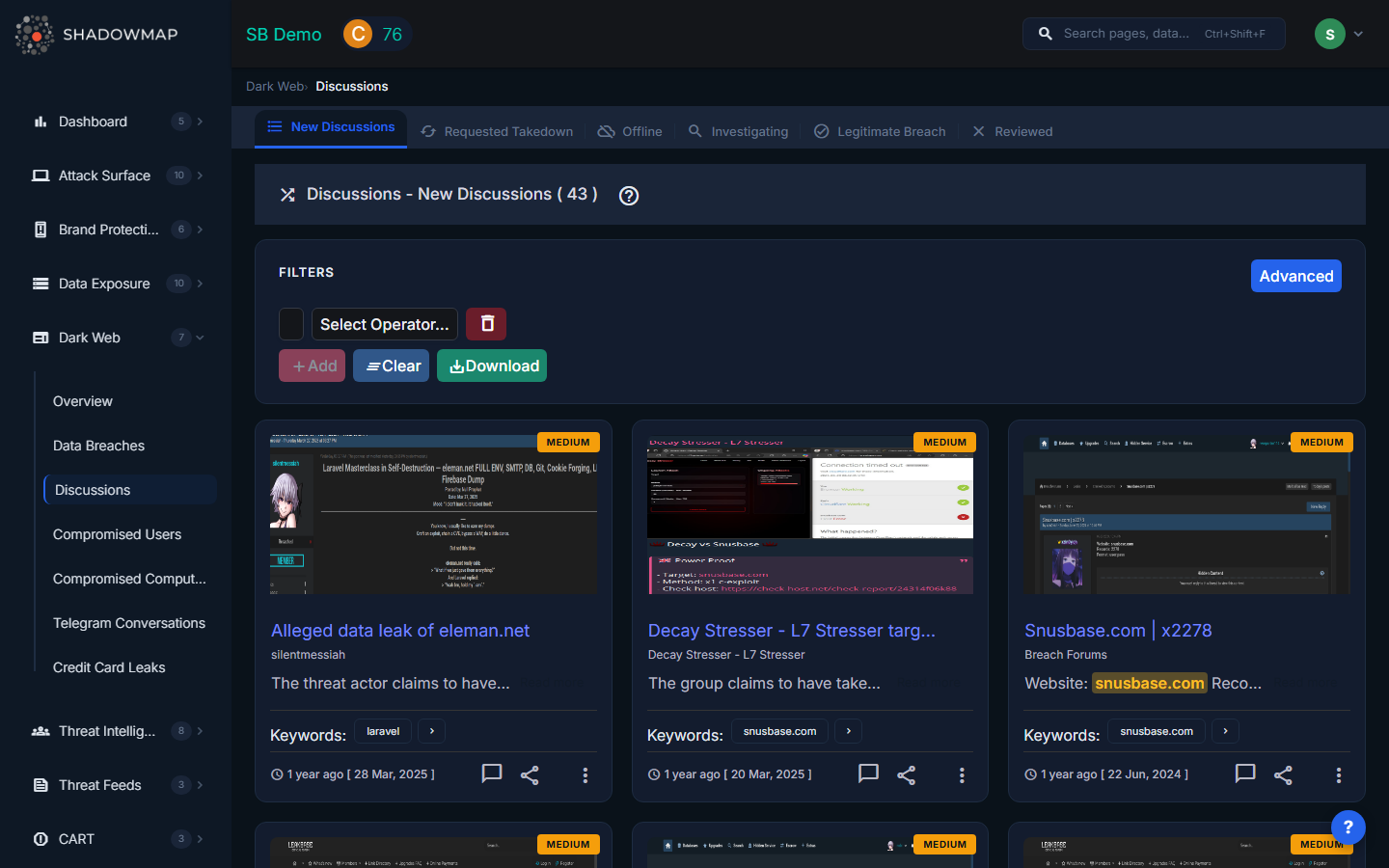
What You See
Each discussion is displayed as a card with:
| Field | Description |
|---|---|
| Severity Badge | Risk level (Critical, High, Medium, Low) based on content analysis and context |
| Screenshot | Captured image of the forum post for visual verification |
| Title | Subject line of the forum post or thread |
| Source | The forum or marketplace where the discussion was found |
| Description | Excerpt of the post content with matched keywords highlighted |
| Keywords | The brand keywords that triggered detection |
| Date | When the post was published on the forum |
| Actions | Comment, share via integration, takedown request, and workflow status options |
What These Discussions May Indicate
Dark web forum posts mentioning your organization typically fall into several categories:
- Selling access -- Initial access brokers advertising RDP, VPN, or shell access to your network. This is an immediate precursor to ransomware or data theft.
- Data for sale -- Threat actors offering databases, credentials, or documents stolen from your organization.
- Vulnerability discussion -- Actors sharing discovered vulnerabilities, misconfigurations, or exposed services in your infrastructure.
- Attack planning -- Coordinated discussions about targeting your organization or industry sector.
- Reputation mentions -- Your brand mentioned in the context of broader discussions (lower severity but worth monitoring).
What to Look For
When reviewing discussions, pay attention to:
- Specificity -- Posts that reference specific systems, IP addresses, employee names, or internal details suggest the actor has already gained some level of access.
- Recency -- Recent posts are more actionable than historical ones.
- Actor reputation -- Well-known actors with established forum histories are more credible than new accounts.
- Supporting evidence -- Posts that include screenshots, sample data, or proof of access are higher priority.
- Pricing signals -- Access being sold cheaply may indicate the actor has already extracted maximum value and moved on. Premium pricing suggests the access is fresh and exclusive.
Actions
- Comment -- Add internal notes for your team's investigation
- Share via Integration -- Push findings to your SIEM, ticketing system, or Slack/Teams
- Takedown Request -- Request removal from the forum (success varies by platform)
- Workflow Status -- Mark as Action Taken, False Positive, or revert to Needs Action
- Export -- Download filtered discussions in Excel format
Filters
Use the search and filter bar to narrow results by:
- Source -- Specific forum or marketplace
- Risk level -- Critical, High, Medium, Low
- Date range -- Focus on recent activity
- Keyword search -- Search within post titles and descriptions
Related
- Telegram Conversations -- Similar monitoring for Telegram channels, which threat actors increasingly prefer over forums
- Dark Web Overview -- Summary of all dark web findings
- Compromised Users (Stealer Logs) -- Access sales often originate from stealer log data
- Alerts -- Configure alerts for new discussion detections
