Compromised Users (Stealer Logs)
ShadowMap monitors stealer log repositories for credentials harvested from your employees' infected machines by info-stealer malware. This is one of the highest-urgency finding types — stealer logs contain active, recently-used credentials that attackers can use immediately.
Overview
How Stealer Logs Work
Info-stealer malware (Redline, Raccoon, Vidar, Lumma, etc.) infects a user's device — often through phishing emails, malicious downloads, or compromised software. Once installed, the malware:
- Extracts saved passwords from all browsers (Chrome, Firefox, Edge)
- Steals session cookies — these can bypass MFA entirely
- Captures autofill data — credit cards, addresses, personal info
- Fingerprints the machine — hostname, OS, hardware ID, IP address
- Packages and uploads everything to a command-and-control server
The stolen data is then sold or shared on dark web marketplaces, Telegram channels, and criminal forums. ShadowMap monitors these sources and alerts you when credentials matching your organization's domains appear.
Why This Is More Dangerous Than Data Breaches
| Factor | Traditional Data Breach | Stealer Log |
|---|---|---|
| Password freshness | Often months/years old | Days to weeks old — likely still valid |
| Session cookies | Not included | Included — can bypass MFA |
| Scope | One breached service | Every service the user accessed |
| Machine access | No device info | Full machine fingerprint — device is actively compromised |
| Password type | Often hashed | Plaintext — no cracking needed |
A stealer log from a single employee can expose credentials to your VPN, email, cloud services, internal tools, and every SaaS application they use — all in plaintext.
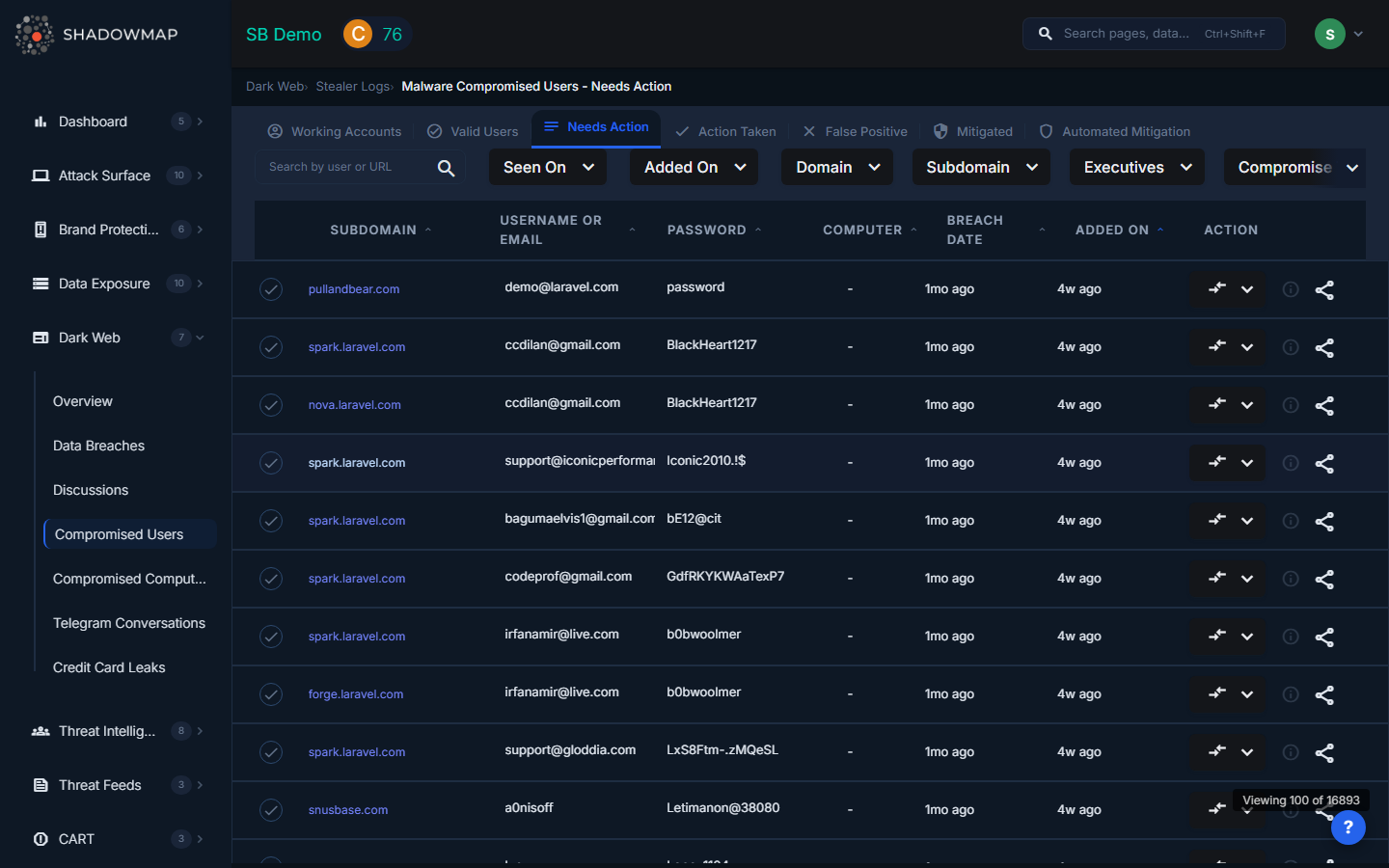
Understanding the Data
| Column | Description |
|---|---|
| Email/Username | The compromised credential's login identity |
| URL | The service the credential was saved for (e.g., vpn.yourcompany.com, mail.google.com) |
| Stealer Family | The malware that harvested the data (Redline, Raccoon, Vidar, Lumma, etc.) |
| Log Date | When the stealer log was generated — more recent = higher urgency |
| Machine | Identifier of the infected machine (hostname, hardware fingerprint) |
| Status | Online (active finding) or actioned |
Incident Response Playbook
When ShadowMap detects stealer log findings for your organization, follow this response workflow:
Phase 1: Immediate Containment (First 4 Hours)
Revoke all active sessions for the affected user across all services
- SSO provider (Okta, Azure AD, Google Workspace) — revoke all sessions
- VPN — disconnect and block the user's VPN access
- Email — revoke OAuth tokens and active sessions
Force password reset on all services the user accesses
- Prioritize: VPN, email, SSO, cloud admin consoles, financial systems
- The stealer log URL list shows which services have saved credentials
Invalidate session cookies — password reset alone is not enough
- Attackers with stolen cookies can bypass MFA
- Regenerate session tokens at the identity provider level
Lock the compromised device
- Use MDM (if managed) to remotely lock or wipe
- If unmanaged (personal device), notify the user immediately
Phase 2: Investigation (24–72 Hours)
Review access logs for the affected user
- Check for logins from unusual IPs or geolocations
- Look for activity during off-hours
- Check for data access patterns that differ from normal behavior
- Focus on the period between the stealer log date and now
Check for lateral movement
- Did the compromised credentials provide access to shared resources?
- Were any admin consoles accessed?
- Check Compromised Computers for the machine showing up in other contexts
Identify the infection vector
- When was the malware installed? (The log date gives an approximate timeline)
- What was the malware family? (Redline vs Raccoon have different distribution methods)
- Was it a phishing email, malicious download, or supply chain compromise?
Phase 3: Remediation (1–2 Weeks)
Re-image the device
- Stealer malware often includes persistence mechanisms
- Do not trust cleaning — re-image from a known-good baseline
- If it's a personal device, advise the user to factory reset
Audit all services in the stealer log
- For each URL in the log, verify: was unauthorized access made?
- Check if any data was exfiltrated from those services
- Reset API keys, tokens, and secrets that were accessible from the device
Enable MFA where missing
- While stolen cookies can bypass MFA, it still raises the bar significantly
- Enforce phishing-resistant MFA (FIDO2/WebAuthn) where possible
Phase 4: Prevention (Ongoing)
Deploy endpoint protection that detects info-stealers
- EDR solutions with behavioral detection (not just signature-based)
- Browser credential storage alternatives (use a password manager instead)
Monitor for recurrence
- Set up an SLA Policy for stealer log findings with immediate escalation
- Re-infection is common if the root cause (phishing, malicious downloads) isn't addressed
User awareness
- Brief the affected user on how the infection occurred
- Update security awareness training to cover info-stealer threats
Connecting Stealer Logs to Other ShadowMap Features
| Feature | Connection |
|---|---|
| Compromised Computers | Same stealer log data, aggregated by machine instead of user — helps identify which devices are infected |
| Leaked Credentials | Traditional breach data — older, often hashed passwords. Stealer logs are more urgent. |
| Data Breaches | Third-party breaches that may include your users' credentials |
| Alerts | Stealer log findings can trigger SLA violations and escalation workflows |
| SLA Policies | Set up automatic notifications for new stealer log detections |
| Security Rating | Stealer log findings affect your Dark Web & Threat Intelligence category score |
Common Questions
Q: How quickly should we respond to a stealer log finding?
Treat stealer logs as a critical incident. The credentials are plaintext and recently used — assume they are being or will be used by attackers. Session revocation and password resets should happen within hours, not days.
Q: If the stealer log is 3 months old, is it still a risk?
Yes. Unless the user has changed their passwords since the log date AND session cookies have expired, the credentials may still be valid. Always verify and reset regardless of age.
Q: We use MFA — are we safe?
Partially. MFA protects against password-only attacks, but stealer logs include session cookies that bypass MFA entirely. The attacker imports the stolen cookie into their browser and has an authenticated session without needing to pass MFA. This is why session revocation is critical.
Q: How is this different from a data breach?
Data breaches expose credentials from a breached third-party service (one service, often old, often hashed). Stealer logs expose credentials from the user's actual browser — every service they've ever saved a password for, in plaintext, with recent timestamps.
Q: Can we prevent stealer logs from appearing?
You can't prevent the dark web from having your data, but you can reduce exposure:
- Discourage saving passwords in browsers (use a password manager instead)
- Deploy EDR with info-stealer detection
- Enforce short session timeouts
- Use phishing-resistant MFA (FIDO2 keys)
Related
- Compromised Computers — Same data, grouped by machine
- Data Breaches — Third-party breach data
- Leaked Credentials — Credentials from public sources
- Dark Web Overview — Summary of all dark web findings
- SLA Policies — Set up automated response workflows
