Security Rating & Scorecard
The Security Rating provides a comprehensive score (0-100) and letter grade (A-F) reflecting your organization's external security posture. It aggregates findings across eight security categories and updates automatically as new scan results come in.
Overview
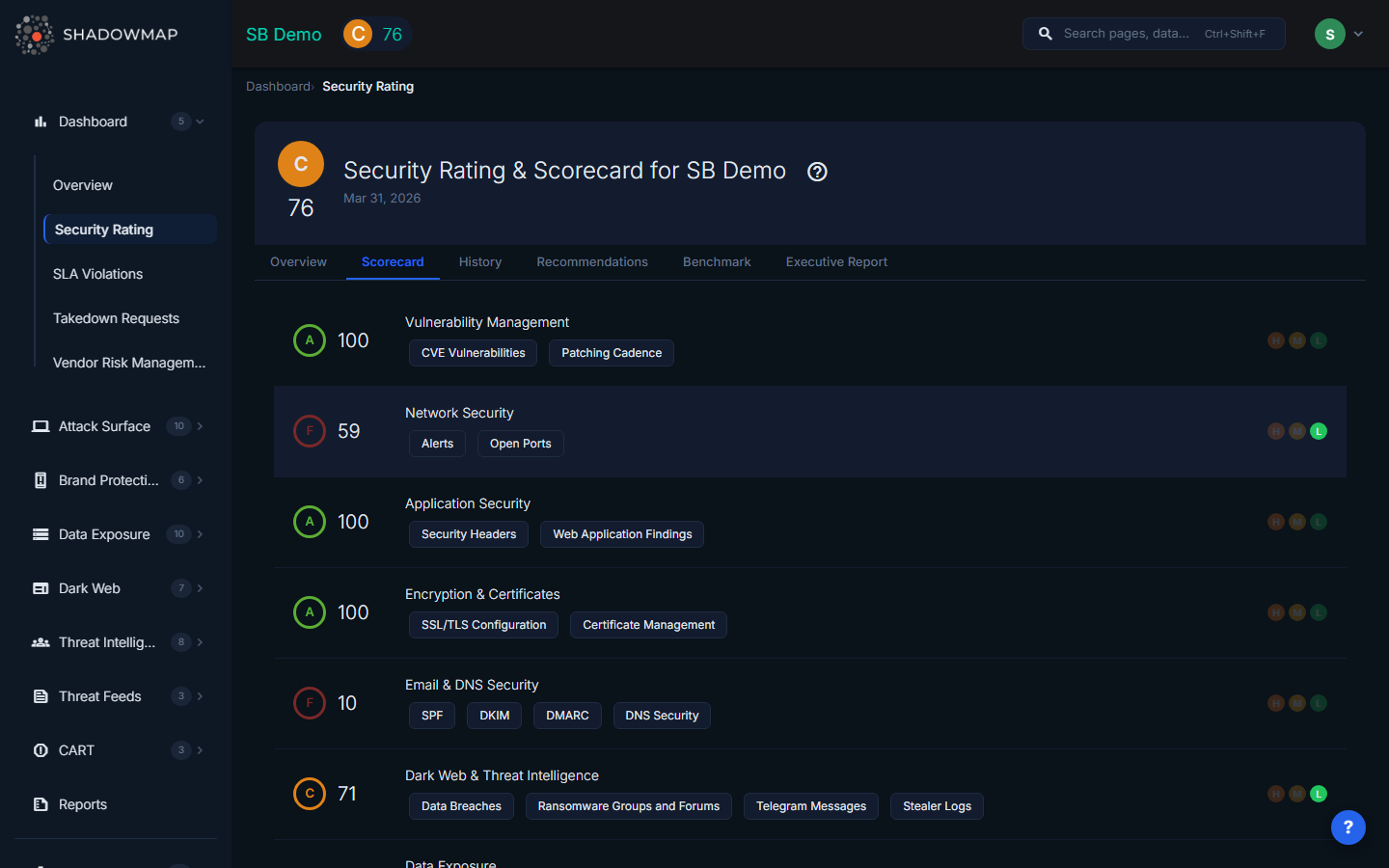
The Security Rating page has five tabs:
- Scorecard — Your current scores across all eight categories
- History — 7-day risk and score trends with weekly/monthly views
- Recommendations — Prioritized actions to improve your score
- Benchmark — Compare your scores against up to 5 peer organizations
- Executive Report — Generate a formatted security posture report
How the Score Is Calculated
Your overall security score is the average of all eight category scores, rounded to the nearest whole number.
Example:
| Category | Score |
|---|---|
| Vulnerability Management | 85 |
| Network Security | 90 |
| Application Security | 72 |
| Encryption & Certificates | 88 |
| Email & DNS Security | 91 |
| Dark Web & Threat Intelligence | 78 |
| Data Exposure | 82 |
| Brand Protection | 84 |
| Overall Score | 84 |
Each category score (0-100) is calculated based on the number and severity of open findings in that domain. Fewer open findings = higher score. Critical and high-severity findings have a larger impact than medium or low findings.
Scores are recalculated automatically when new scan results arrive (typically every few hours). The displayed score reflects the most recent calculation.
Grade Scale
| Grade | Score Range | Color |
|---|---|---|
| A | 90 – 100 | Green |
| B | 80 – 89 | Gold |
| C | 70 – 79 | Orange |
| D | 60 – 69 | Red |
| F | 0 – 59 | Dark Red |
The Eight Security Categories
Each category monitors a specific domain of your external attack surface. The sub-modules listed under each category show exactly what data feeds into that score.
1. Vulnerability Management
Measures known vulnerabilities in your exposed infrastructure.
- Feeds from: Open alerts by severity, CVE findings, open port risks
- Improve by: Patching critical and high-severity vulnerabilities, closing unnecessary open ports
2. Network Security
Assesses the security of your network-facing infrastructure.
- Feeds from: Open ports, network service configurations, exposed services
- Improve by: Closing unnecessary ports, hardening service configurations
3. Application Security
Evaluates the security posture of your web applications.
- Feeds from: Web application findings, misconfigurations, security header issues
- Improve by: Fixing application misconfigurations, adding security headers, addressing web app vulnerabilities
4. Encryption & Certificates
Monitors SSL/TLS configurations and certificate health.
- Feeds from: SSL certificate issues, TLS configuration problems, certificate expiry
- Improve by: Renewing expiring certificates, disabling weak TLS versions (1.0, 1.1), fixing certificate chain issues
5. Email & DNS Security
Assesses email and DNS security configurations.
- Feeds from: SPF, DKIM, DMARC configurations, DNS security issues
- Improve by: Configuring DMARC with enforcement, fixing SPF records, enabling DNSSEC
6. Dark Web & Threat Intelligence
Tracks your organization's exposure on the dark web.
- Feeds from: Data breaches, dark web discussions, Telegram conversations, executive credential leaks
- Improve by: Forcing password resets for breached accounts, investigating and closing dark web discussion mentions, monitoring stealer log findings
7. Data Exposure
Monitors for leaked data across public sources.
- Feeds from: Code repositories, Docker containers, S3 buckets, leaked APIs, leaked files
- Improve by: Removing exposed code repositories, securing S3 buckets, revoking leaked API keys, remediating Docker container exposures
8. Brand Protection
Tracks brand abuse and impersonation.
- Feeds from: Phishing URLs, fake mobile applications, domain squatting
- Improve by: Requesting takedowns for phishing sites, reporting fake apps to app stores, monitoring squatted domains
Reading the Scorecard
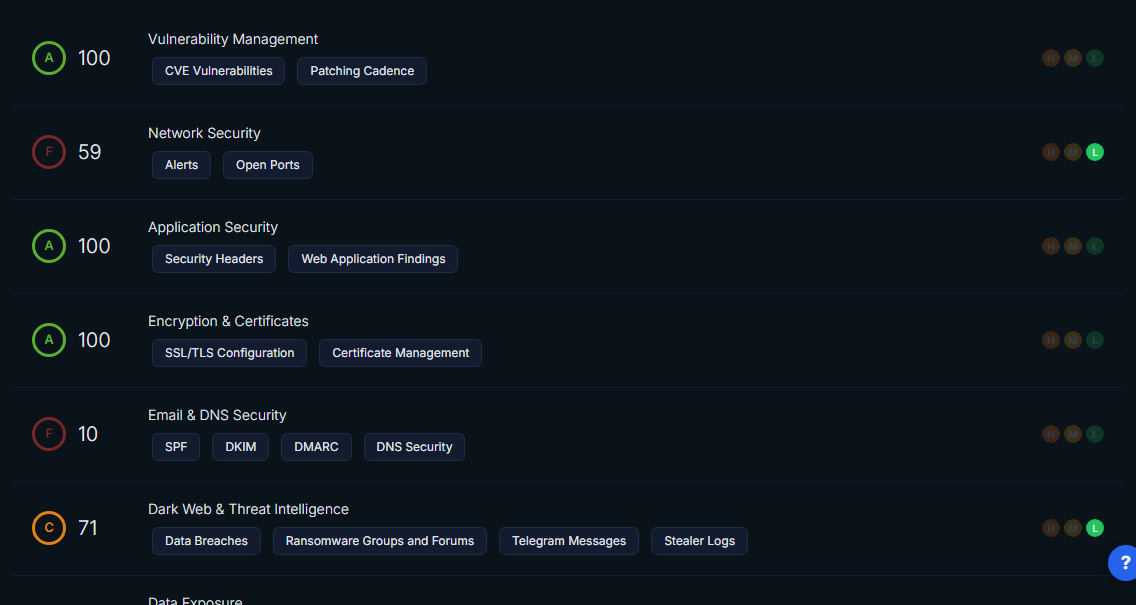
Each category card on the Scorecard tab shows:
- Grade badge — Color-coded letter grade (A-F) for this category
- Category name — Which security domain this covers
- Sub-module chips — The specific data sources feeding into this score (e.g., "CVE Vulnerabilities", "Patching Cadence")
- Risk indicators — Colored dots showing whether there are High (red), Medium (orange), or Low (blue) severity findings. Dimmed dots mean no findings at that severity level.
- Score — The numeric score (0-100) for this category
History Tab
The History tab shows how your security posture has changed over time with two charts:

Risk Trend (Line Chart)
Shows the count of High, Medium, and Low severity findings over the past 7 days. Use this to spot:
- Sudden spikes in findings (new scan revealed issues)
- Gradual decline (remediation efforts working)
- Persistent high counts (unaddressed chronic issues)
Score Trend (Bar Chart)
Shows your daily average score with bars color-coded by grade. Use this to:
- Track score improvements after remediation
- Identify which days saw score changes
- Correlate score changes with specific remediation activities
Navigate between weeks using the Previous and Next buttons. Switch between Daily, Weekly, and Monthly views for different time horizons.
Recommendations Tab
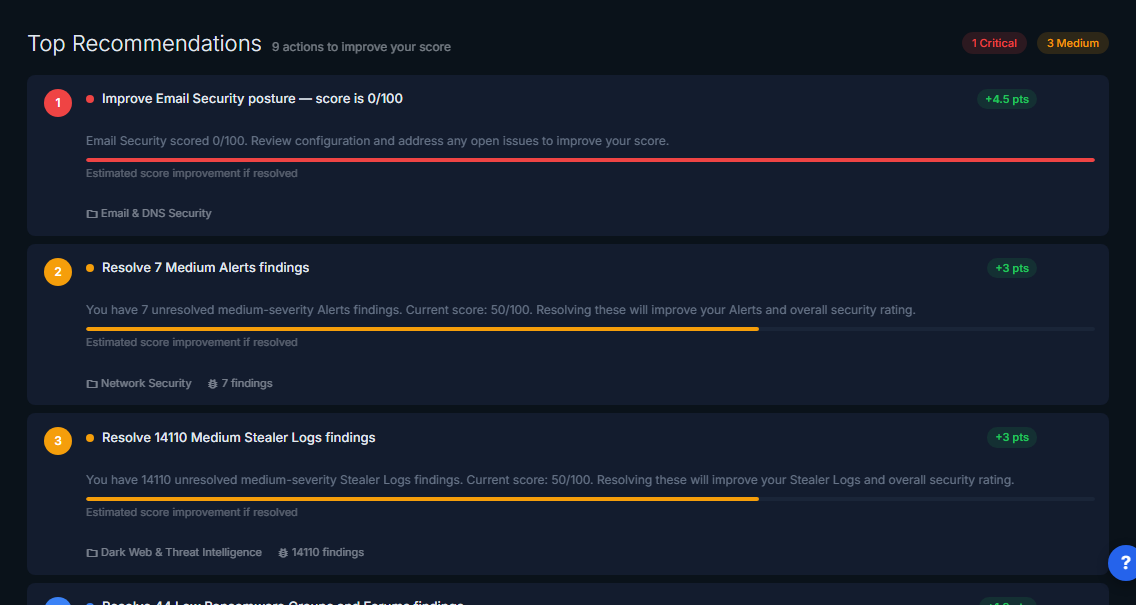
ShadowMap generates prioritized recommendations to improve your security score. Each recommendation includes:
| Field | Description |
|---|---|
| Category | Which security module this relates to |
| Title | What needs to be fixed |
| Description | Detailed explanation and context |
| Severity | Critical, High, Medium, or Low |
| Affected Count | Number of assets impacted |
| Estimated Score Impact | How many points your score could improve |
| Priority | Ranking order (1 = most impactful) |
Working with Recommendations
Recommendations have four statuses:
- Open — Not yet addressed (default)
- In Progress — Being worked on
- Resolved — Fixed and verified
- Dismissed — Accepted risk or not applicable
To update a recommendation's status, click on it and select the new status. Resolved and dismissed recommendations are removed from the active list.
TIP
Focus on recommendations with the highest Estimated Score Impact first. Resolving a single critical recommendation can improve your overall score by several points.
Benchmark Tab
Compare your security posture against up to 5 peer organizations.
Adding a Peer for Comparison
- On the Benchmark tab, click Add Customer (or the "+" card)
- Search for the organization you want to compare against
- Select them from the dropdown
- Their scores appear alongside yours, ranked by overall score
Reading the Benchmark
- Your organization is highlighted with a distinct background
- Each peer shows their overall score and category breakdown
- Use this to understand where you stand relative to industry peers
- Assign priority (High/Medium/Low) and tags to categorize peers
Removing a Peer
Click the remove icon next to a peer's name to remove them from your benchmark list.
WARNING
Benchmark data is based on ShadowMap's external scanning of those organizations. It reflects their externally visible security posture, not their internal security controls.
Improving Your Score
Here is a prioritized approach to improving your security rating:
Quick Wins (Days)
- Renew expiring SSL certificates — Certificates expiring within 30 days drag down your Encryption & Certificates score
- Configure DMARC — If your domains lack DMARC enforcement, your Email & DNS Security score is penalized
- Close unnecessary open ports — Each exposed port with no business justification reduces your Network Security score
Medium-Term (Weeks)
- Patch critical CVEs — Address CVEs in CISA's KEV catalog first. These have the highest score impact in Vulnerability Management
- Remove exposed code repositories — Leaked code with credentials is a high-severity Data Exposure finding
- Request takedowns for phishing sites — Active phishing sites significantly impact your Brand Protection score
Ongoing
- Force password resets for breached accounts — Each credential found in breach databases affects your Dark Web & Threat Intelligence score
- Monitor and respond to new findings — SLA-compliant response times demonstrate mature security operations
- Review and act on recommendations — The Recommendations tab prioritizes actions by score impact
Common Questions
Q: My score dropped suddenly. Why?
Your score recalculates when new scan results arrive. A score drop typically means:
- New findings were discovered in a scan (check Alerts for recent items)
- A previously expiring certificate has now expired
- New leaked credentials or code repositories were found
- A new data breach was published that includes your organization
To investigate, navigate to the category that dropped on the Scorecard tab and check its sub-modules for new findings.
Q: How often does the score update?
Scores recalculate automatically when new scan data arrives, typically every few hours. The timestamp next to your score shows when the current rating was calculated. There is a 10-minute cache, so changes may take up to 10 minutes to appear.
Q: Why do I have different scores than I expected?
Your score is based on externally visible findings only. ShadowMap scans your organization from the outside — the same perspective an attacker would have. Internal security controls, compensating controls, and remediation that isn't visible externally won't be reflected in the score.
Q: Can I dispute or adjust a finding that's affecting my score?
Yes. Navigate to the specific finding in the relevant module (e.g., Alerts, Data Exposure) and mark it as Accepted Risk or False Positive. This will exclude it from your score calculation on the next recalculation.
Q: How do I share my security rating with stakeholders?
Use the Executive Report tab to generate a formatted report. You can also:
- Take a screenshot of the Scorecard tab
- Export historical data from the History tab
- Set up automated reports via Settings > Integrations
Q: What's the difference between the score on the Dashboard Overview and the Security Rating page?
They show the same score. The Dashboard Overview has a gauge widget summarizing your overall score, while the Security Rating page provides the full breakdown by category, history, recommendations, and benchmarking.
Deep Dives
- How Scoring Works — Full methodology: category weights, severity multipliers, geometric mean, recency decay
- Improving Your Score — Prioritized action plan: quick wins, medium-term, ongoing practices
- Benchmarking — Compare your scores against peer organizations
Related
- Dashboard Overview — The gauge widget on the main dashboard shows your overall score
- Alerts — Open alerts affect your Vulnerability Management and other category scores
- Vulnerability Overview — CVEs directly impact your Vulnerability Management score
- Data Exposure Overview — Leaked data affects your Data Exposure category score
- Dark Web Overview — Breach data affects your Dark Web & Threat Intelligence score
- SSL Certificates — Certificate issues affect your Encryption & Certificates score
- Vendor Risk Management — VRM uses the same scoring methodology to rate your vendors
