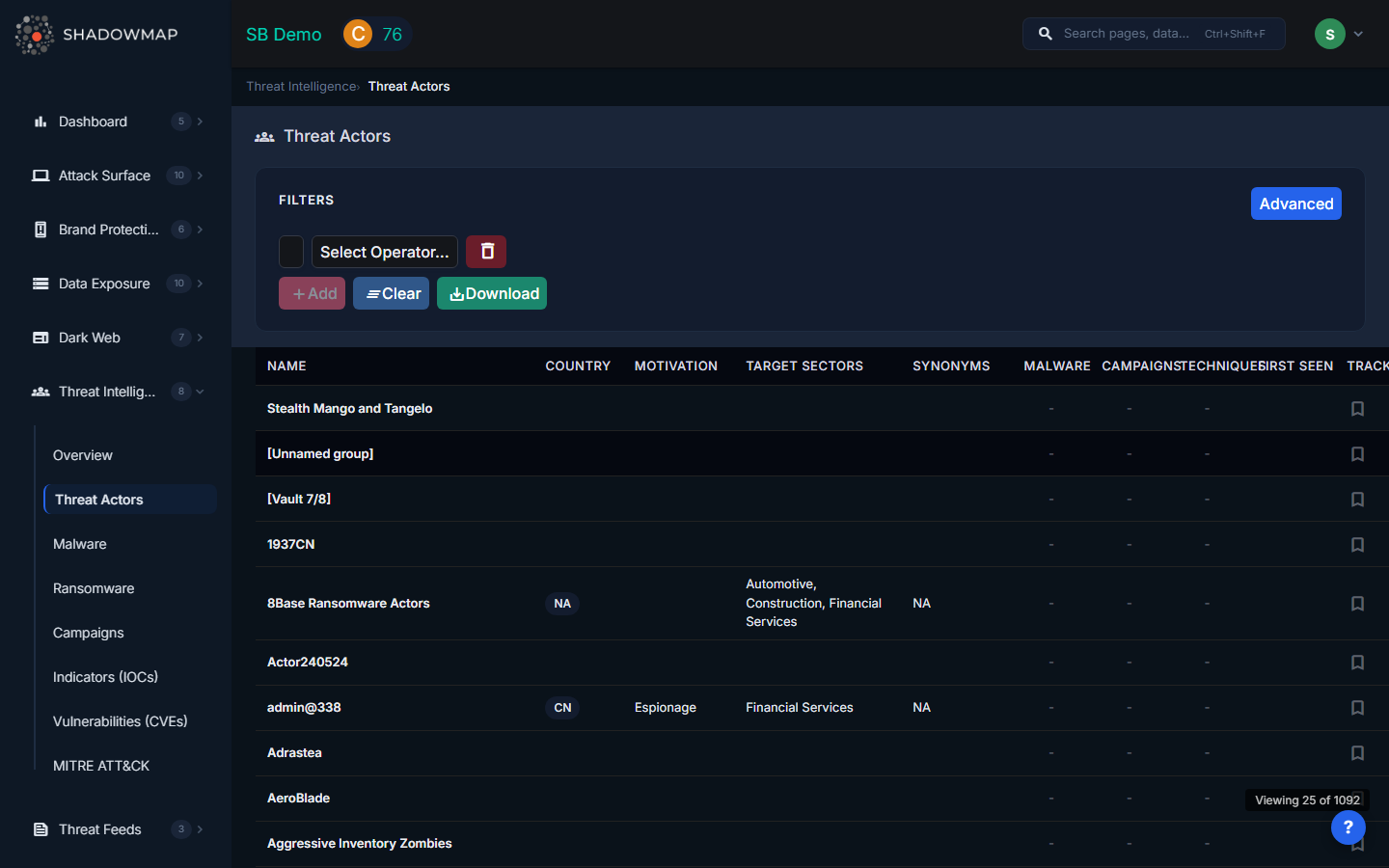
Threat Actors
ShadowMap maintains profiles of APT groups, cybercriminal organizations, hacktivists, and other threat actors. Each profile aggregates intelligence from MISP galaxy clusters to show the actor's origin, motivation, target sectors, associated malware, campaigns, and ATT&CK techniques -- giving your team the context needed to assess whether a specific actor poses a risk to your organization.
Overview
Understanding the Data
The threat actor list displays the following columns:
| Column | Description |
|---|---|
| Name | Primary name of the threat actor (e.g., APT29, Lazarus Group, FIN7) |
| Country | Country of origin or attribution (displayed as a tag) |
| Motivation | Primary motivation: financial gain, espionage, disruption, ideology, or unknown |
| Target Sectors | Industries this actor is known to target (shows top 3; full list in detail view) |
| Synonyms | Alternative names used by other vendors (shows top 2; full list in detail view) |
| Malware | Count of malware families associated with this actor |
| Campaigns | Count of known campaigns or operations attributed to this actor |
| Techniques | Count of MITRE ATT&CK techniques observed in this actor's operations |
| First Seen | Earliest known activity date for this actor |
| Track | Bookmark icon to track/untrack this actor for dashboard widgets and alerts |
Click any row to view the full threat actor profile, including detailed descriptions, full synonym lists, all associated malware, campaigns, techniques, and IOCs.
Filters
Use the filter bar to narrow the list:
| Filter | Options |
|---|---|
| Country | Filter by actor's country of origin |
| Motivation | Financial, Espionage, Disruption, Ideology |
| Target Sector | Filter by the industries the actor targets |
| Resource Level | Government, Organization, Individual -- indicates the actor's sophistication and resources |
| Search | Free-text search across actor names, synonyms, and descriptions |
Track / Bookmark Feature
Click the bookmark icon on any actor to track them. Tracked actors:
- Appear in your dashboard's Tracked Actor Activity widget
- Help prioritize threat intelligence relevant to your organization
- Can be used to build a watchlist of actors relevant to your industry
Export
Click the export button to download the current filtered view as an Excel file. The export respects all applied filters and search terms.
How to Use Threat Actor Intelligence
- Risk assessment -- Identify actors that target your industry and region. Cross-reference their TTPs with your defensive capabilities.
- Purple teaming -- Use actor TTPs to design realistic attack simulations. Focus on techniques from actors in your sector.
- Executive briefing -- Filter by your sector and summarize the top actors, their motivations, and recent activity for leadership.
- Detection engineering -- Navigate from an actor to their techniques (ATT&CK), then build detection rules covering their known methods.
- Incident response -- When investigating an incident, search for matching IOCs, malware, or TTPs to attribute activity to a known actor.
Related
- Malware -- Malware families used by threat actors
- Campaigns -- Operations attributed to threat actors
- MITRE ATT&CK -- Technique coverage mapped from actor TTPs
- Threat Intelligence Overview -- Summary dashboard with sector-specific actor analysis
- Indicators of Compromise -- Search for IOCs associated with specific actors
